
Data Discovery
Get industry-leading data discovery & classification for your sensitive data - accurately and at scale.
Learn more
Get industry-leading data discovery & classification for your sensitive data - accurately and at scale.
Learn more
Get AI ready and accelerate data security, privacy, compliance, and hygiene for AI to accelerate adoption and minimize risk.
Learn more
Data Security Posture Management done differently - from uncovering dark data to surfacing critical risk to remediation.
Learn More
Data Privacy Management with data-driven automation for regulatory compliance and privacy by design.
Learn More
From data collection to destruction, AI data management to get more from your data.
Learn More
Reduce risk and align with data regulations and security frameworks, avoid audits, and enable compliance.
Learn More
Reduce insider risk and manage insider threats with access governance controls and get to a least privileged model.
Learn More
Automatically identify & label the data that matters most and enforce policies across your environment.
Learn MoreAutomatically (and accurately) scan, find, and classify the data that matters most to you - wherever it lives, whatever it is, at petabyte scale.
Uncover dark data, identify high risk data, and take action for security, compliance, privacy, and governance for modern data lifecycle management.
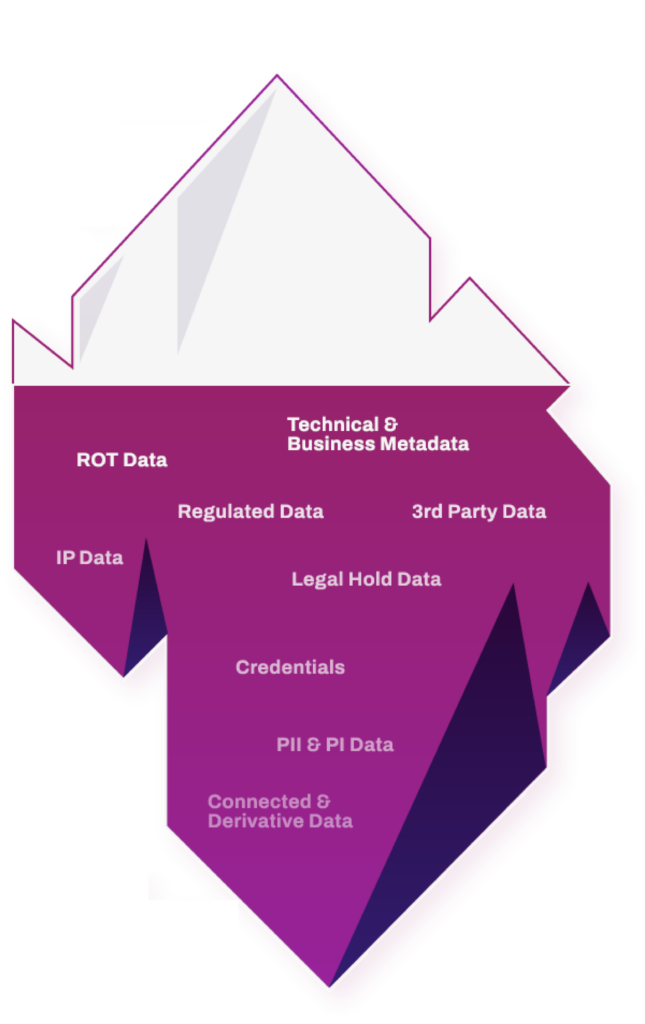
Understand, monitor, and minimize data risk wherever your data lives - with more coverage across cloud, on-prem data centers, and everywhere in between.
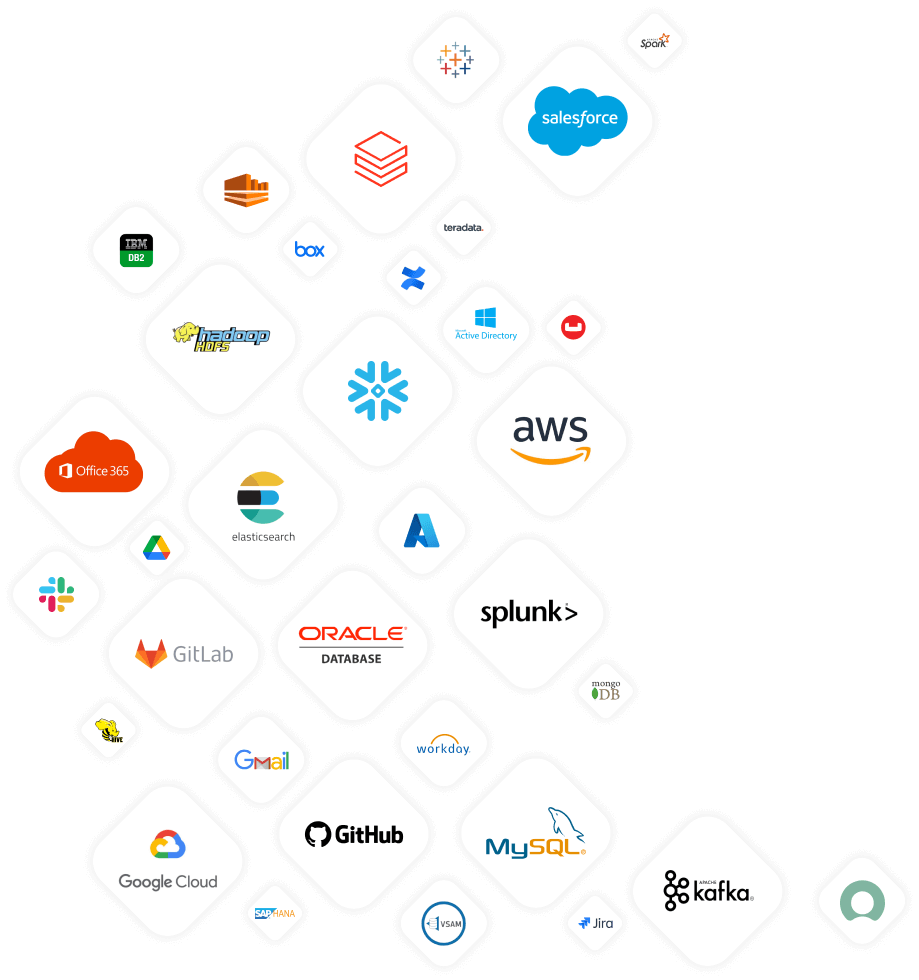
Easily integrate across your ecosystem to get more from the modern tech stack - and make better decisions around your unstructured, structured, and semi-structured data.

Lock down high risk data, reduce risk, and automate controls and enforcement around sensitive data
Learn More
Map, monitor, and mitigate internal and external access based on data sensitivity and role
Learn More
Migrate the right data, with the right controls, to the right place - in the right way
Learn More
Manage what data is shared by whom; audit and enforce policies on data usage for AI
Learn More
for privacy regulations and security frameworks (GDPR, CCPA, NIST, HITRUST, Cross border transfers, SEC reqs, and more)
Learn More
Take a data-driven approach to privacy-by-design and automatically fulfill privacy compliance requirements
Learn More
Make better decisions and understand your data for faster disposition in M&A, regulatory audits, and due diligence.
Learn More
Automate data visibility and control, reduce the attack surface, minimize your data footprint, and get more value from your data
Learn More
Reduce OpEx and CapEx by automatically eliminating similar, duplicate, and ROT data; minimize the attack surface automatically
Learn MoreModern architecture design to scale with your data at petabyte scale - without affecting business or systems.
Advanced ML that nobody else has - from customizable NLP classifiers to graph tech for more depth & accuracy.
Deploy where you want: in the cloud, on prem, or across a hybrid environment - agentless & automated.

RBAC, Password Vault Support, Minimum Privileges, 2FA, Secure Cloud Deployment, No data duplication.
Choose the apps you need and build from there - with apps for privacy, security, and governance.

Integrate with your tech stack with partner apps or build your own on an open, API-first platform.

BigID Named Market Leader: Data Security Posture Management
Get a custom demo with our data experts in privacy, protection, and perspective – and see BigID in action.