Automated Data Rights Fulfillment
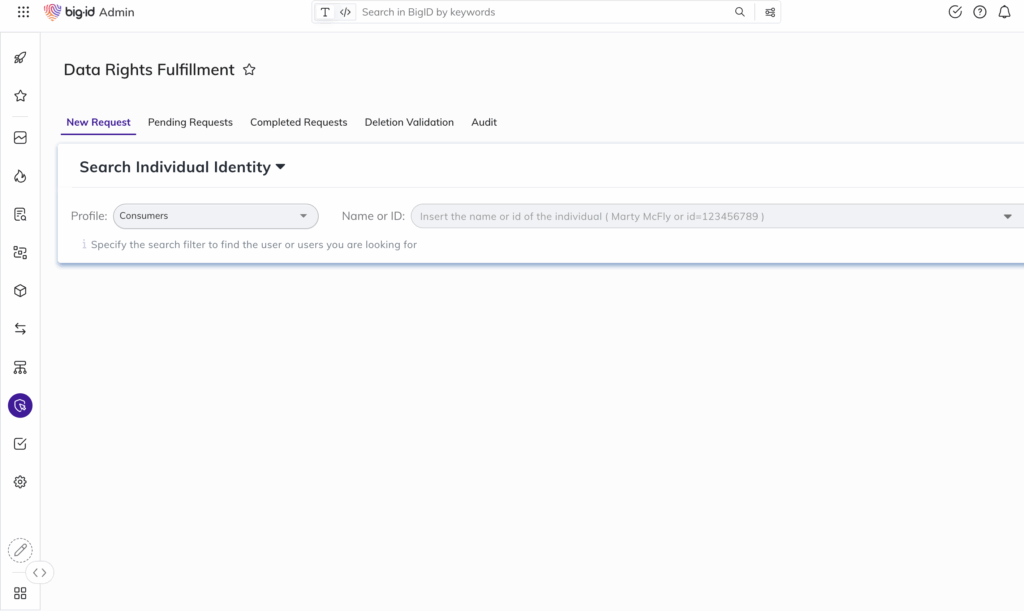
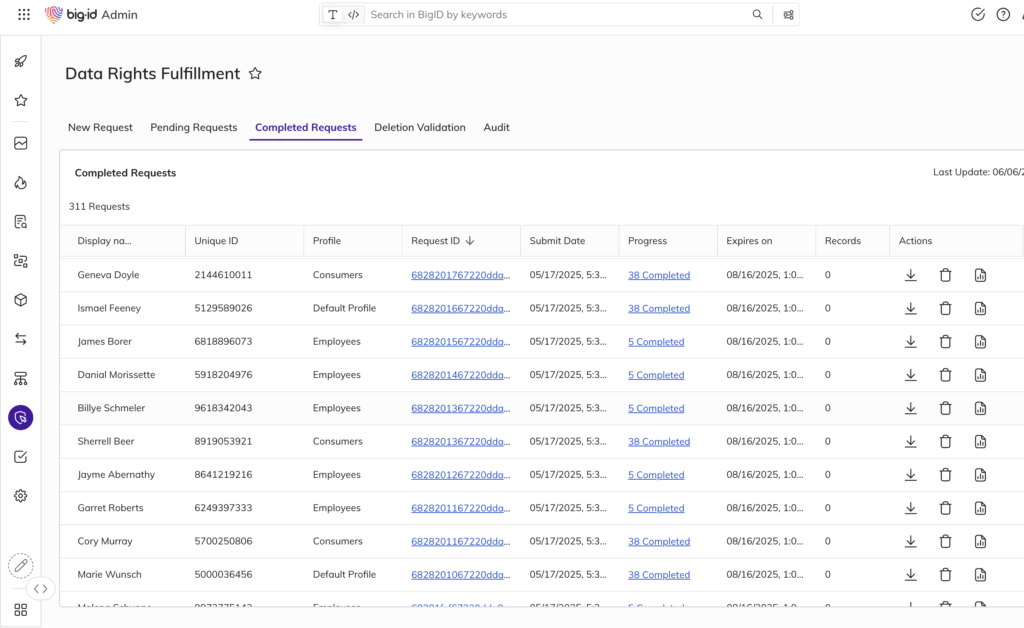
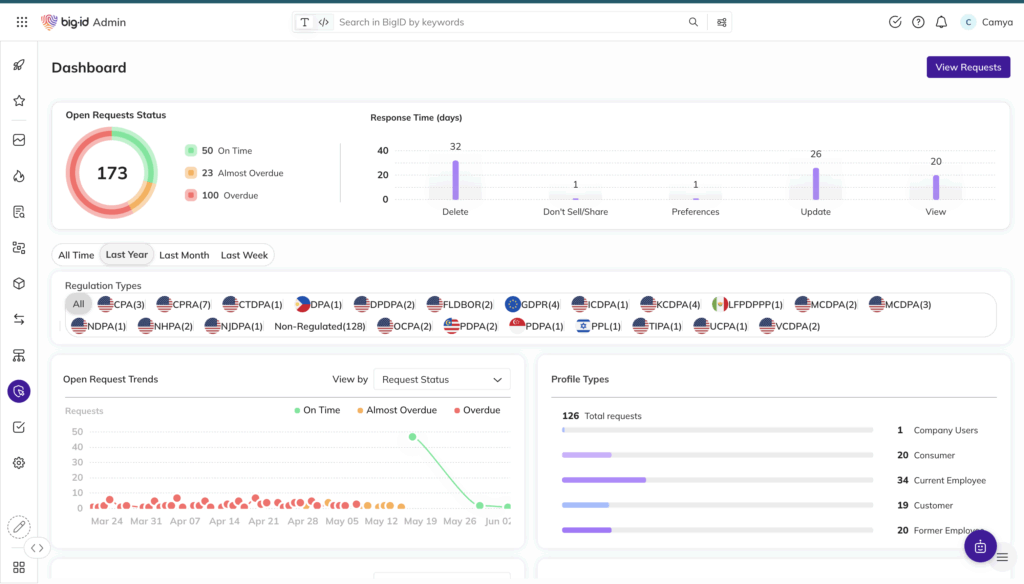
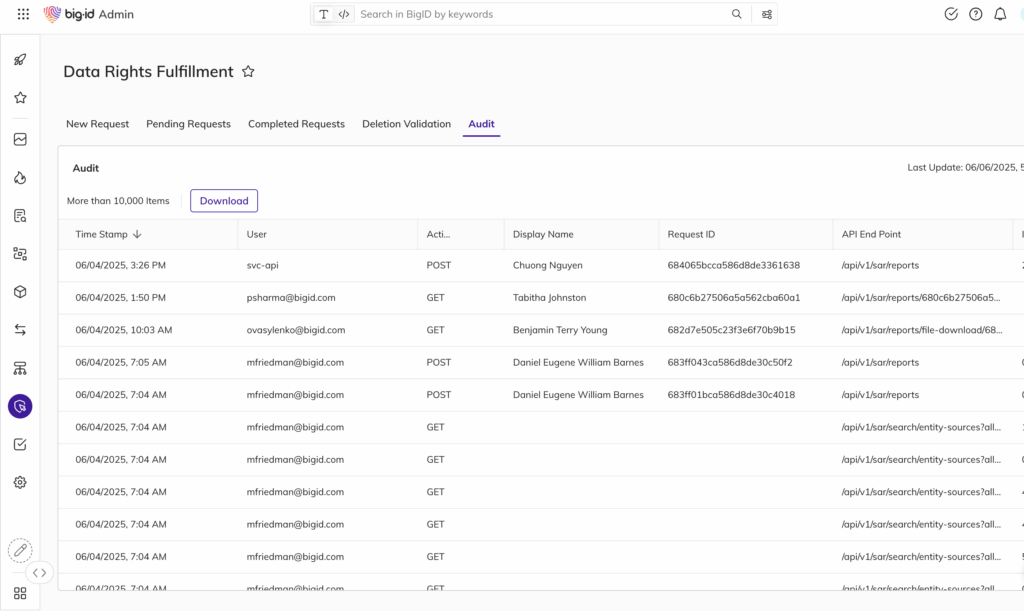
- Respond to access and deletion requests with automated, auditable workflows
- Fulfill “right to be forgotten” with direct integration to deletion execution
- Reduce manual workload and response time with intelligent orchestration