Automated Privacy Impact Assessments
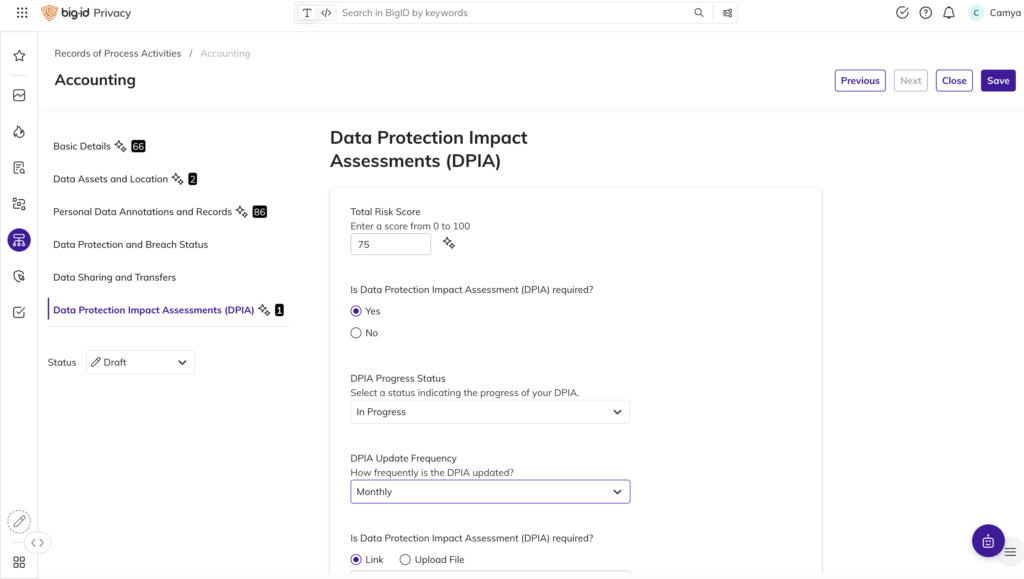
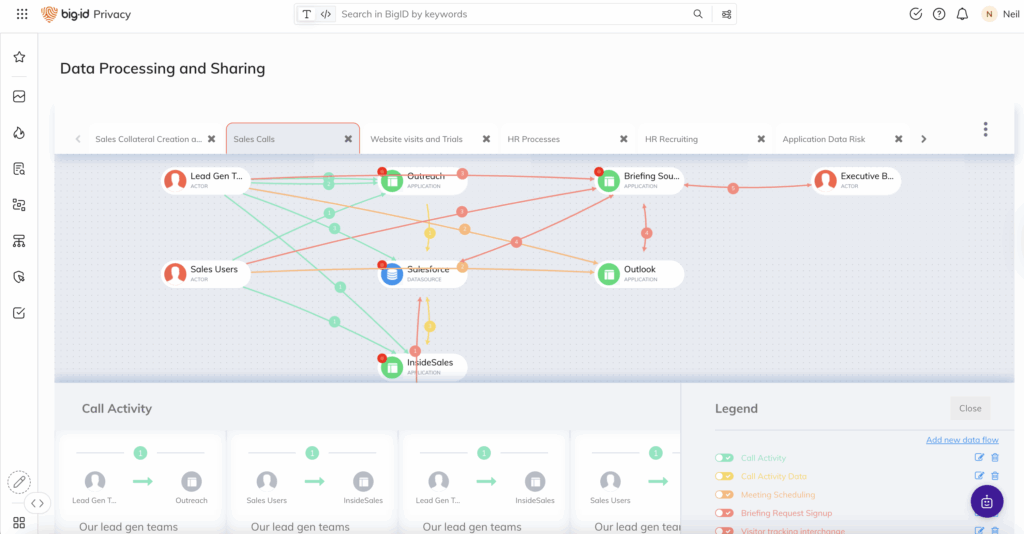
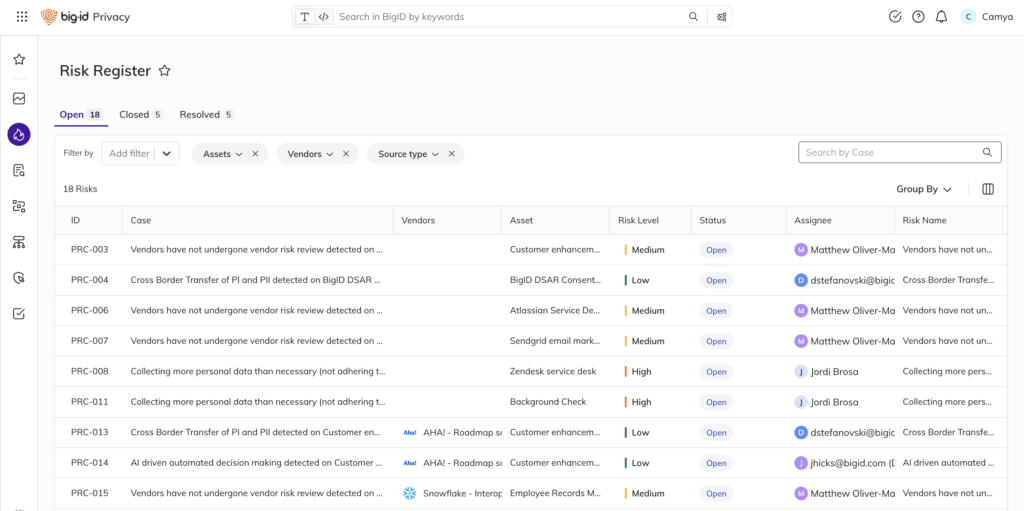
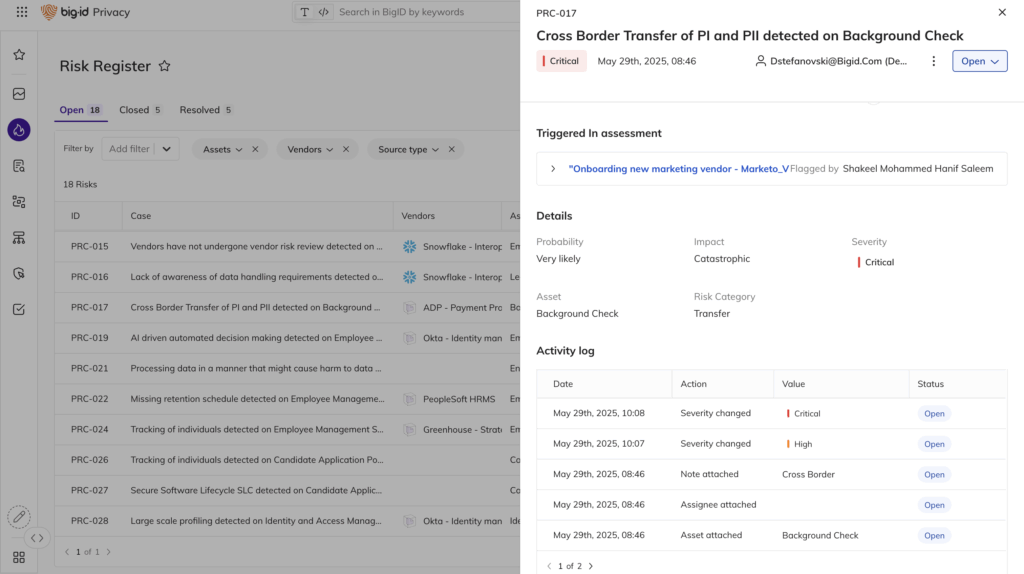
- Create assessments tailored for new products, data use cases and processing activities
- Customize templates and workflows for specific business units or regulatory needs
- Reduce bottlenecks and manual follow-ups with dynamic routing and status tracking