Cyber resilience is crucial for all businesses, regardless of their size or industry. In today’s digital age, organizations rely heavily on technology to store, process, and share sensitive information, making them vulnerable to cyber attacks and data breaches. Therefore, it is essential to have a strong cyber resilience strategy to protect against such threats.
What is cyber resilience?
Cyber resilience refers to an organization’s ability to prepare for, respond to, and recover from cyber attacks or data breaches. It involves implementing measures and procedures that enable an organization to withstand and quickly recover from a cyber attack or security incident while minimizing the impact on operations and data security.
Data security and privacy professionals play a critical role in building and maintaining cyber resilience within their organizations. They must assess the organization’s existing security posture and identify potential vulnerabilities that could be exploited by attackers. They must also develop and implement robust security controls and procedures to prevent cyber attacks and limit the damage in the event of a breach.
In addition to technical measures, cyber resilience also involves preparing and training employees to identify and respond to security incidents. This includes conducting regular security awareness training to ensure that employees are aware of the latest threats and know how to report suspicious activity.
Ultimately, cyber resilience is about building a culture of security within an organization. By taking a proactive and holistic approach to cybersecurity, data security and privacy professionals can help their organizations stay one step ahead of cyber threats and ensure that sensitive data remains secure.
Why is cyber resilience important?
One of the key benefits of cyber resilience is enhanced data security. By implementing robust security controls and procedures, organizations can minimize the risk of data breaches and unauthorized access to sensitive information. This not only protects the organization’s reputation and financial wellbeing but also helps to maintain trust with customers, partners, and stakeholders.
Cyber resilience also plays a critical role in ensuring data privacy. With the increasing number of data breaches and cyber attacks, data privacy has become a major concern for businesses and individuals alike. By prioritizing cyber resilience, organizations can better protect their customers’ personal data and ensure compliance with data privacy regulations.
Furthermore, cyber resilience supports effective data governance. By establishing clear policies and procedures for data management, organizations can ensure that data is collected, stored, and processed in a secure and compliant manner. This promotes transparency and accountability while reducing the risk of data breaches and other security incidents.
In summary, cyber resilience is essential for businesses to protect their data, maintain trust with customers, and comply with data privacy regulations. By prioritizing cyber resilience, data security and privacy professionals can help their organizations stay resilient against the ever-evolving threat landscape and ensure the secure and responsible use of data.
Uncovering the challenges of cyber resilience
Cyber resilience poses significant challenges that organizations must address to protect their systems and data from cyber threats. These challenges include:
- Rapidly evolving threats: Cyber threats are constantly changing, and organizations must keep up with the latest tactics and techniques used by attackers. This requires continuous monitoring and analysis of cyber threats and vulnerabilities.
- Complexity of IT systems: Modern IT systems are complex and interconnected, making it challenging to identify and address vulnerabilities. Organizations must have a comprehensive understanding of their IT systems and be able to manage and secure them effectively.
- Lack of skilled personnel: There is a shortage of skilled cybersecurity personnel, making it difficult for organizations to find and hire the talent they need to manage their cyber resilience effectively.
- Cost: Building and maintaining a strong cyber resilience program can be expensive. Organizations must be prepared to invest in cybersecurity tools and technologies, as well as in training and education for their personnel.
- Compliance requirements: Organizations must comply with various regulatory requirements related to data protection and privacy. Meeting these requirements can be challenging, particularly as regulations continue to evolve.
- Third-party risk: Organizations are often reliant on third-party vendors and service providers, which can introduce additional cyber risks. Organizations must ensure that their third-party providers meet the same.
In summary, many organizations struggle to allocate sufficient resources to cybersecurity, which can leave them vulnerable to attacks. Achieving and maintaining cyber resilience requires a proactive and adaptive approach to cybersecurity, as well as ongoing education and investment in cybersecurity measures.
5 steps to becoming cyber resilient
Becoming cyber resilient is crucial for security professionals to protect their organizations from cyber threats. Here are the steps they can take to improve cyber resilience:
- Identify risks and vulnerabilities: Security professionals should identify the risks and vulnerabilities that their organization faces. This involves conducting a thorough risk assessment and identifying the weak points in their organization’s network, systems, and applications.
- Develop a response plan: After identifying the risks and vulnerabilities, security professionals should develop a response plan that outlines the steps to take in the event of a cyber attack. The plan should include incident response procedures, communication protocols, and steps to minimize the impact of an attack.
- Implement security controls: Security professionals should implement security controls such as firewalls, intrusion detection systems, and encryption to prevent unauthorized access to their organization’s systems and data. They should also ensure that their organization’s software and hardware are regularly updated to address new threats.
- Train employees: Security professionals should provide regular cybersecurity training to all employees to raise awareness of cyber threats and teach best practices for avoiding them. This includes teaching employees how to create strong passwords, how to recognize phishing emails, and how to securely handle sensitive data.
- Test and refine: Security professionals should regularly test their organization’s cyber resilience by conducting penetration testing and vulnerability assessments. This helps identify weaknesses in their organization’s security posture and allows them to refine their response plan and security controls accordingly.
The role of digital transformation in cyber resilience
Digital transformation plays a critical role in enhancing an organization’s cyber resilience. Here are some ways in which digital transformation can improve cyber resilience:
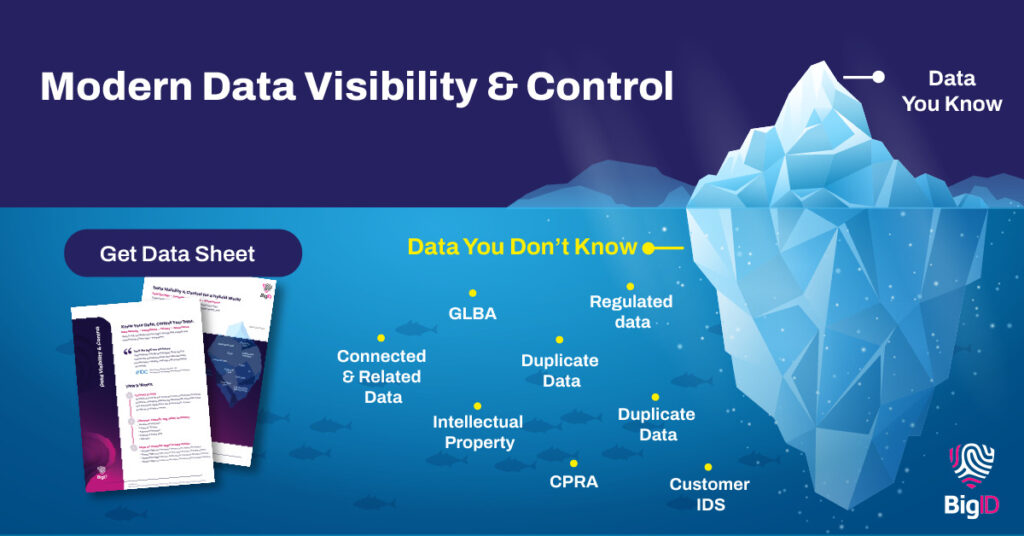
- Enhanced visibility: Digital transformation allows organizations to gain better visibility into their network and data, which is essential for identifying potential cyber threats. With the help of modern tools and technologies, security professionals can easily monitor their organization’s network and identify suspicious activities.
- Automation: Automation is an integral part of digital transformation, which can be utilized to streamline security operations and response procedures. By automating repetitive tasks such as patching, updates, and backups, organizations can reduce the risk of human errors and respond quickly to potential cyber threats.
- Cloud adoption: Cloud computing has become a game-changer for many organizations, as it enables them to scale their operations quickly and efficiently. However, cloud adoption also introduces new security challenges. By embracing digital transformation, organizations can implement robust security controls and monitoring tools to ensure their cloud infrastructure is secure.
- Data protection: Digital transformation provides organizations with the ability to collect, process, and store vast amounts of data. However, this also means that organizations need to implement robust data protection measures to prevent data breaches. With digital transformation, security professionals can leverage modern technologies such as encryption, access controls, and data loss prevention to secure their organization’s data.
- Agile response: Digital transformation enables organizations to adopt an agile approach to cybersecurity, allowing them to quickly respond to new and emerging cyber threats. By leveraging real-time threat intelligence and automation, organizations can proactively identify and respond to potential cyber threats, reducing the impact of any attack.
In summary, digital transformation is essential for organizations to enhance their cyber resilience. By embracing new tools and technologies, organizations can improve their visibility, automate security operations, protect their data, and respond quickly to cyber threats.
BigID’s Approach to Cyber Resilience
BigID is an industry leading data discovery platform for privacy, security, and governance. Using machine learning and advanced AI technologies, BigID automatically and accurately discovers, scans, identifies, and classifies all your sensitive data stored both on prem and throughout the hybrid cloud. BigID’s intuitive platform gives you a comprehensive view of all your most valuable assets, allowing you to glean better insights and proactively manage and safeguard your enterprise data.
The Security Suite includes a variety of powerful tools like the Data Remediation App which helps organizations manage remediation for high risk, sensitive, and regulated data— giving them the confidence to take the appropriate action and minimize impact. Along with the Breach Data Investigation App, organizations can quickly identify compromised data, where and who was impacted and streamline incident response.
To see how BigID can increase your organization’s cyber resilience and protect all of your most valuable data— schedule a free 1:1 demo today.