What is the Principle of Least Privilege (PoLP) Access?
Least privilege access limits access rights or permissions of users, applications, and systems to only what is necessary for them to perform their specific tasks. It’s a computer security principle under identity and access management (IAM) that grants users access solely to the data, systems, and resources necessary for their job functions, while denying them access to anything beyond that.
What is Privilege Creep?
Often, users are given access to high-value data or systems but their rights are not revoked when they don’t need it anymore. They might have been given elevated privileges such as administrator because the IT team granted blanket permissions for convenience.
Their role might have changed but their access permission were never reviewed. As a result, they now have additional access rights. They might have been given what was supposed to be temporary access. However, these short-term rights were never revoked.
Privilege creep refers to this phenomenon where users keep getting privileged credentials or additional access without their existing privileges being reviewed, which results in access over and above their needs.
Your business can improve its security posture by building in PoLP access and reviews into your information security protocol. You can also combine these with just-in-time access to prevent privilege creep.
Why Implement the Least Privilege Access (LPA) Principle?
Limit Insider Threats
Data breaches aren’t always caused by malicious actors. Sometimes, they can be due to insider threats or critical systems and network access being granted to people who don’t require it. Least-privilege access helps reduce the risk of unauthorized access, data breaches, and cyber attacks.
By restricting access to only what is necessary, organizations can better control and monitor their systems and data, reducing their attack surface. It helps reduce attack surfaces by minimizing the risk of human error, intentional misuse, or accidental exposure.
PoLP access is often combined with role-based access control, where users are granted access depending on what they need to fulfill their job.
Comply With Regulations
Data security regulations and standards, such as HIPAA, PCI DSS, and GDPR, require you to have adequate measures in place to protect sensitive information and personal data of your customers. Least privilege principle is one of the methods that you can implement to show you’re doing your due diligence.
Cybersecurity Policy Enforcement
For cybersecurity professionals, enforcing the principle of LPA is essential to their job. They must ensure that access control policies and procedures are in place and that all users follow them. Regularly reviewing and auditing user access is also necessary to ensure that permissions remain current and no unnecessary privileges are granted.
Least privilege access is a critical security principle that organizations and cybersecurity professionals should prioritize to protect their systems, data, and reputation.
Principles of Least Privilege (POLP)
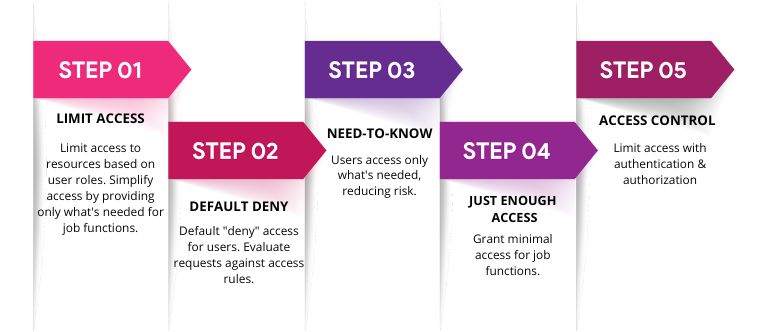
The following are the best practices of LPA:
- Limit Access: LPA should provide appropriate levels of access to resources, data, or systems based on the role and responsibility of each user. In simpler terms, the system should only provide users access to the required resources to complete their required tasks.
- Default Deny: Under LPA, the default position is to deny users access to a resource. When a user requests access to a resource, the access control system evaluates the request against a set of rules that determine whether the request should be granted. This is similar to the zero trust network access (ZTNA) framework, where it is assumed that no user or device can be trusted by default.
- Need-to-Know: Users are granted access to only what they need to know to perform their tasks. This ensures that sensitive data or resources are only accessed by authorized individuals, reducing the risk of data breaches.
- Just Enough Access: Grant users the minimum permission and access required to the information required to complete a task rather than giving users full access to resources.
- Access Control: Use access control mechanisms to limit access based on policies and rules set up by administrators. Access control mechanisms include authentication, authorization, and accounting (AAA) systems designed to ensure that users can access only the resources they are authorized to access.
Implement Least Privilege Access to Prevent Security Breaches
According to the 2024 Verizon Data Breach Investigations Report, 68% of breaches involved a non-malicious human element, such as mistakes or falling for social engineering attacks. The Cost of a Data Breach Report from IBM found that the average cost of a data breach was $4.88 million. 94% of organizations experienced email security incidents, with 70% of account takeover (ATO) attacks starting as phishing attempts.
LPA can help limit the damage that can be done by attackers who gain access through a successful phishing attack. It can help mitigate the impact of credential theft by limiting the access that an attacker can obtain with stolen credentials. Here’s how you can implement the principle of least access.
- Audit your environment to review roles and access for overprivileged access credentials.
- Remove local administrator privileges for those who don’t need it.
- Create separate administrator accounts from standard accounts, and monitor privileged user sessions for anomalous activities.
- Use a digital vault to provision administrator access credentials.
- Change administrator passwords after use to prevent stolen passwords from keylogging software and pass-the-hash attacks.
- Implement just-in-time access privileges, allowing users to access the information needed to complete their tasks.
- Monitor identity and access management privileges in cloud environments, such as AWS, Azure, and Google Cloud platforms and remove permissions that aren’t needed.

Least Privilege Access Examples
The principle of LPA can be applied across a wide range of industries and verticals. Here are some examples of how it can be used in different industries:
- Healthcare: In the healthcare industry, LPA is critical for protecting sensitive patient data. Access should be limited to only those healthcare professionals who need access to the patient data to provide care. For example, nurses and doctors may need access to patient data, while administrative staff may not.
- Finance: In the finance industry, LPA protects financial data and reduces the risk of fraud. Access should be limited to only those employees who need access to the financial data. For example, financial advisors need client financial data, while administrative staff don’t.
- Government: In the government sector, least privilege is foundational in protecting sensitive data and national security. Access should be limited to only individuals with access requirements. For example, classified information must be limited to individuals with a security clearance.
- Education: In the education sector, LPA is important for protecting student data and ensuring privacy. For example, teachers need student data to provide personalized instruction, but not the administrative staff.
- Manufacturing: In the manufacturing industry, LPA is important for protecting intellectual property and trade secrets. For example, engineers may need access to design files, while factory workers may not require access.
Zero Trust Least Privilege
Zero trust and least privilege are two related concepts that aim to improve cybersecurity by limiting access to data, systems, and resources. Zero trust is a security model that assumes that all users, devices, and applications are potential threats and should be verified before being granted access to resources. Least privilege is the practice of limiting user access to only what is necessary to what they need to do their job.
The concept of zero trust least privilege involves combining these two security principles to create a more secure environment. This approach is based on the idea that users should be allowed to see the data, systems, and resources that they need to perform their job functions, and access should be granted on a case-by-case basis, rather than assuming that users should have access to everything by default.
While the zero trust least privilege concept can improve security, there are also some concerns and challenges associated with implementing it:
- Implementation complexity: Implementing zero trust least privilege can be complex and time-consuming. It requires a thorough analysis of the organization’s systems and data, as well as the development of granular access policies and controls.
- User experience: Zero trust least privilege can make the user experience more cumbersome, as users may need to request access to resources on a case-by-case basis, rather than having access automatically granted.
- Resource-intensive: The implementation of zero trust least privilege may require additional resources, such as increased staffing and more advanced technologies, to effectively monitor and control access to resources.
- Integration challenges: Integrating zero trust least privilege with existing systems and applications can be challenging, as it may require significant changes to the underlying architecture and infrastructure.
- Compliance requirements: Zero trust least privilege may also raise compliance concerns, as some regulations and standards may require certain levels of access to be granted by default, which may conflict with the principle of least privilege.
While there are some concerns and challenges associated with implementing zero trust least privilege, this security approach can improve security by reducing the risk of data breaches and cyber attacks. It is important for organizations to carefully consider the risks and benefits of this approach and implement it in a way that aligns with their specific needs and requirements.

BigID’s Approach to Least Privilege Access
Data is your most valuable asset and is what your adversaries are ultimately after. Implementing a least privilege model and establishing a zero trust architecture starts with knowing your data. BigID gives organizations complete data visibility and control in order to get to a least privilege model. BigID’s data-centric approach to zero trust combines deep data discovery, next-gen data classification, and risk management.
Know where this data is located, how sensitive it is, and who’s accessing it to understand over exposed data and users or groups with excessive privilege to sensitive data. Automatically carry out remediation on datasets, sources, and files, as well as on users and groups. Quickly target violations and revoke file access rights and permissions to sensitive or critical data. These insights enable security teams to define and enforce rigid policies around sensitive data to mitigate unwanted exposure and use, wherever that data lives— throughout the entire data lifecycle.
To start bolstering your data security posture and implement a least privilege access model across your data landscape, schedule a free 1:1 demo with BigID today.