DSPM vs CSPM: Understanding the Difference Between Data Security Posture Management and Cloud Security Posture Management
Protecting sensitive data and maintaining a robust security posture reduces the risk of data breaches and unauthorized access. Two essential components of a comprehensive cybersecurity strategy are data security posture management (DSPM) and cloud security posture management (CSPM).
While both DSPM and CSPM prevent security incidents and protect data, they serve different purposes and operate in distinct environments.
Understanding the DSPM vs CSPM is crucial for organizations looking to strengthen their security measures effectively.

Data Security Posture Management (DSPM)
DSPM offers protection for an organization’s sensitive data, regardless of its location. It provides a centralized platform for security teams to manage, monitor, and enhance the security posture of their enterprise data. It identifies sensitive data and classifies it, detects vulnerabilities and misconfigurations, assesses security needs, and consistently enforces policies.
DSPM solutions offer key features like data discovery, protection, and security controls. Some DSPM tools employ advanced scanning techniques to locate and categorize sensitive data across various stores, including on-premises databases, file servers, and multi-cloud environments. This granular visibility enables security teams to assess potential risks and apply appropriate security controls to mitigate them effectively.
Cloud Security Posture Management (CSPM)
CSPM focuses on network security and cloud environments, where organizations increasingly store their data and run critical applications. With the rapid adoption of public cloud infrastructure and Software-as-a-Service (SaaS) apps, ensuring cloud data security has become paramount.
CSPM tools offer comprehensive visibility into the security state of cloud infrastructure and services. They provide insights into potential security risks, such as publicly accessible resources, weak authentication mechanisms, or misconfigured storage buckets. They help organizations maintain a robust data and cloud security posture by continuously monitoring configurations, assessing compliance with security policies, and detecting vulnerabilities or misconfiguration to reduce data risk.
By actively scanning cloud data and infrastructure, CSPM solutions enable organizations to identify and address security gaps before they can be exploited by attackers.
Key Differences Between CSPM and DSPM
While both data security and cloud security posture management share the goal of enhancing security posture, their key differences are in scope and focus. CSPM encompasses all data sources, regardless of location or storage medium, whereas DSPM concentrates exclusively on securing cloud environments.
CSPM solutions concentrate on securing cloud infrastructure and services, such as virtual machines, containers, serverless functions, and cloud storage. They monitor and enforce security best practices specific to cloud environments.
In contrast, DSPM solutions are designed to address the challenges of securing data across diverse systems, including on-premises databases, file servers, and even if the data is stored in the cloud. They enable organizations to enforce data protection policies, manage access controls, and ensure compliance with data privacy regulations.

CSPM vs DSPM: Which Security Strategy is Right For You?
Both data security and cloud security posture management offer unique benefits and considerations. Understanding their strengths and limitations is crucial for when organizations devise their cybersecurity strategy.
Pros of DSPM:
- Comprehensive coverage: DSPM provides a holistic view of an organization’s data security posture, encompassing on-premises and cloud environments.
- Granular data visibility: These tools offer deep insights into sensitive data, enabling organizations to classify, locate, and protect valuable information effectively.
- Consistent security policies: DSPM platforms allow organizations to establish and enforce security policies consistently across their data sources, ensuring compliance and minimizing vulnerabilities.
Cons of DSPM:
- Limited to data sources: Since DSPM does not address the specific security challenges associated with cloud environments, it could potentially leave organizations vulnerable in those areas.
- Resource-intensive implementation: Implementing DSPM solutions across diverse data stores and systems may require substantial resources and integration efforts.
Pros of CSPM:
- Cloud-specific expertise: CSPM can help address the unique security requirements of cloud environments with specialized features and best practices.
- Real-time monitoring: These tools continuously monitor cloud infrastructure and services, enabling organizations to detect and respond promptly to security threats and vulnerabilities.
- Compliance assurance: CSPM helps organizations assess and maintain compliance with industry regulations and security standards specific to the cloud.
Cons of CSPM:
- Limited to cloud environments: Since CSPM solutions do not encompass data stored in on-premises systems, they potentially leave blind spots in an organization’s overall security posture.
- Complexity of cloud infrastructure: Cloud environments’ dynamic and complex nature can make CSPM implementation and configuration challenging, requiring specialized expertise.
Use Cases for DSPM and CSPM
DSPM and CSPM solutions can be applied in various scenarios, depending on an organization’s specific needs and security requirements.
Functions of DSPM:
- Data protection and privacy: DSPM solutions are crucial in securing sensitive data, ensuring compliance with data privacy regulations, and protecting against unauthorized access.
- Data discovery and classification: DSPM tools help organizations identify and classify sensitive data, enabling them to prioritize security efforts and allocate resources effectively.
Functions of CSPM:
- Cloud infrastructure security: CSPM solutions help organizations monitor and secure cloud infrastructure, ensuring adherence to security best practices, and detecting unauthorized activities or misconfigurations.
- Compliance management: CSPM tools assist in assessing and maintaining compliance with cloud-specific security standards and regulations, such as the CIS Benchmarks or the General Data Protection Regulation (GDPR).
Can the Two Be Used Together to Mitigate Data Security Risks?
Absolutely! Even though the two have distinct focuses, they are complementary. By using both solutions, organizations can achieve a comprehensive security posture management strategy that covers both on-premise data and cloud environments.
Data security and cloud security can be integrated to provide a unified view of an organization’s security posture, combining insights from both data assets and cloud infrastructure. This integrated approach allows security teams to detect and respond to potential threats more effectively, leveraging the strengths of each solution.
Because CSPM focuses on securing hybrid and multi-cloud environments, and DSPM focuses on securing physical data repositories, CSPM and DSPM together are a more optimized approach for improving total security posture across an organization.
When to Combine CSPM and DSPM
Organizations should consider combining these two solutions when they have a multifaceted security landscape that encompasses both data on-premise and cloud environments.
If an organization extensively uses cloud infrastructure and services to store and process sensitive data, integrating data security posture management and cloud security posture management solutions is highly recommended. This combined approach ensures comprehensive security coverage, minimizes blind spots, and enhances the overall cybersecurity posture.
BigID’s approach to DSPM and CSPM
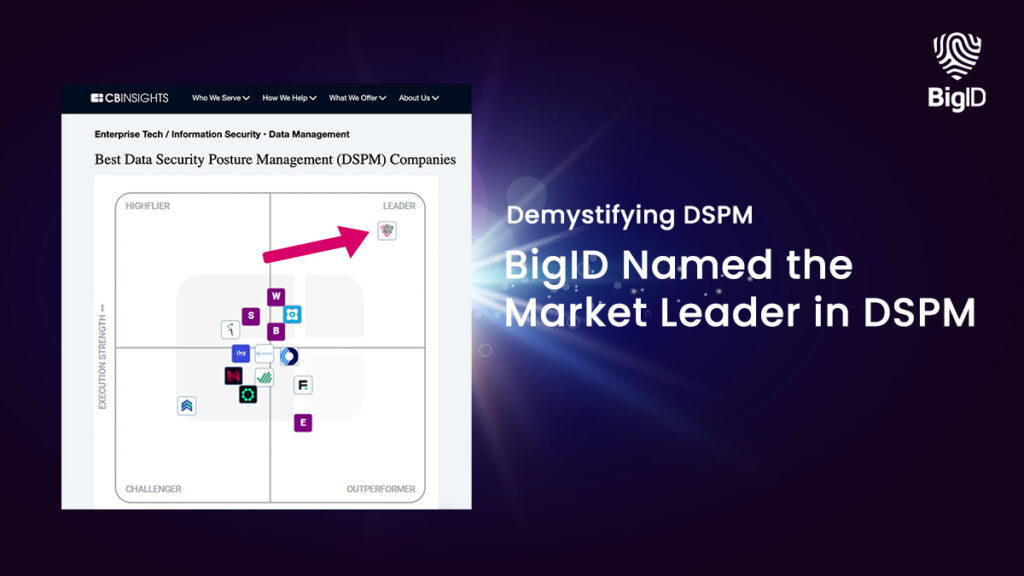
Understanding the difference between DSPM and CSPM is crucial for organizations seeking to enhance their cybersecurity posture. BigID is the leading provider of data management for privacy, security, and governance offering scalable solutions that combine the two.
BigID’s comprehensive platform offers organizations a unified view of their security posture, bringing together insights from data assets and cloud environments. With deep data discovery and classification, you can accurately and automatically scan and identify all your sensitive data.
Manage and proactively assess risk for sensitive data both on-prem and in the cloud with BigID’s Security Suite. Prevent unauthorized access and secure your enterprise infrastructure from end to end.
To strengthen your organization’s security posture, learn how to reduce data access risks by downloading our datasheet.