UK enterprises run on cloud.
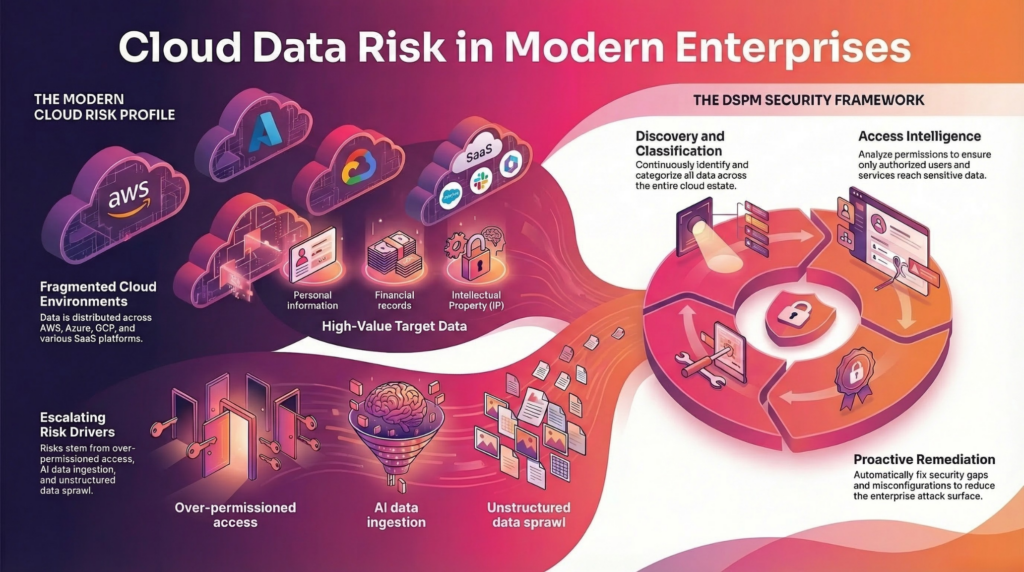
Teams deploy workloads across AWS, Azure, and Google Cloud. Employees collaborate through SaaS platforms like Microsoft 365 and Google Workspace. Data flows across environments faster than security teams can track it.
This shift creates a new challenge:
Sensitive data spreads across cloud environments without clear visibility or control.
Security teams cannot protect what they cannot see.
That is why UK organizations are turning to Data Security Posture Management (DSPM) to secure cloud data at scale.
At a Glance
• Sensitive data spreads across multi-cloud and SaaS environments without clear visibility.
• Traditional cloud security tools focus on infrastructure, not data.
• DSPM helps teams discover, classify, and secure sensitive data across cloud environments.
• Organizations reduce exposure and shift cloud security from reactive to proactive.
Best for: Cloud security leaders and architects.
What is DSPM for Cloud Security?
DSPM for cloud security helps organizations discover sensitive data across cloud and SaaS environments, analyze access risk, and reduce data exposure before incidents occur.
The Cloud Data Security Problem UK Enterprises Face
Cloud adoption has solved infrastructure challenges. It has also introduced data risk.
Sensitive data now lives across:
- multi-cloud environments
- SaaS applications
- collaboration platforms
- data lakes and analytics systems
- AI pipelines
Each environment creates its own access model, storage structure, and risk profile.
Security teams struggle to answer basic questions:
- Where does sensitive data exist in our cloud environments?
- Which cloud assets expose regulated data?
- Who can access sensitive data across SaaS platforms?
- Which data flows into AI systems?
Without visibility, data exposure risk grows silently across cloud environments.
Why Traditional Cloud Security Tools Falls Short
Most cloud security tools focus on infrastructure:
- misconfigurations
- network exposure
- workload vulnerabilities
These tools do not focus on the data itself.
They cannot tell you:
- what sensitive data exists in cloud storage
- where regulated data resides
- who has access to critical information
This creates a dangerous gap.
Organizations secure infrastructure while sensitive data remains exposed.
What DSPM Brings to Cloud Security
DSPM shifts the focus from infrastructure to data.
It gives security teams the ability to:
- discover sensitive data across cloud and SaaS environments
- classify regulated and high-risk data
- analyze access to that data
- reduce exposure before incidents occur
This creates a complete view of data risk across the cloud.
Multi-Cloud Visibility Without Blind Spots
UK enterprises rarely operate in a single cloud.
Teams store data across:
- AWS S3 buckets
- Azure Blob Storage
- Google Cloud Storage
- SaaS platforms
Each platform creates visibility gaps.
DSPM closes those gaps.
Security teams can:
- scan data across all environments
- identify sensitive data regardless of location
- maintain consistent classification policies
This eliminates fragmented visibility.
Securing SaaS Data at Scale
SaaS platforms hold some of the most sensitive enterprise data.
Examples include:
- customer data in CRM systems
- financial records in shared documents
- confidential communications in collaboration tools
These environments grow rapidly and often lack governance.
DSPM helps organizations:
- discover sensitive data across SaaS platforms
- identify overexposed files and folders
- detect excessive sharing and permissions
Security teams gain control over data that previously remained invisible.
Reducing Data Exposure Risk in Cloud Environments
Cloud data exposure rarely comes from a single failure.
It comes from accumulation:
- unused data remains in storage
- permissions expand over time
- data spreads across environments
DSPM helps reduce exposure by enabling teams to:
- identify high-risk data repositories
- remove unnecessary access
- eliminate redundant sensitive data
- enforce retention policies
This transforms cloud security from reactive to proactive.
DSPM and AI Data in the Cloud
AI systems increasingly rely on cloud data.
Organizations feed data from cloud storage into:
- training datasets
- analytics pipelines
- RAG systems
Without governance, sensitive data flows directly into AI systems.
DSPM helps prevent that.
Security teams can:
- identify sensitive data before it enters AI pipelines
- apply classification and controls
- reduce the risk of AI data exposure
This becomes critical as AI adoption grows across UK enterprises.
Operationalizing Cloud Data Security with DSPM
Effective cloud data security requires a structured approach.
Step 1: Discover Data Across Cloud Environments
Scan all cloud and SaaS platforms to identify sensitive data.
Step 2: Classify Data with Context
Understand what data exists and why it matters.
Step 3: Analyze Access
Identify who can access sensitive data and where risk exists.
Step 4: Remediate Risk
Remove access, secure data, and enforce governance policies.
This approach allows security teams to continuously manage cloud data risk.
Frequently Asked Questions About DSPM for Cloud Security
1. What is DSPM for cloud security?
DSPM for cloud security helps organizations discover sensitive data across cloud and SaaS environments, classify it, analyze access risk, and reduce exposure before incidents occur.
2. Why is DSPM important for multi-cloud environments?
Multi-cloud environments create fragmented visibility. DSPM provides a unified view of sensitive data across AWS, Azure, Google Cloud, and SaaS platforms, allowing security teams to manage risk consistently.
3. How does DSPM differ from traditional cloud security tools?
Traditional cloud security tools focus on infrastructure, such as misconfigurations and network exposure. DSPM focuses on the data itself, showing what data exists, where it resides, and who can access it.
4. What types of data can DSPM discover in cloud environments?
DSPM discovers structured and unstructured data, including personal data, financial records, intellectual property, regulated data, and sensitive business information across cloud storage and SaaS platforms.
5. How does DSPM reduce data exposure in the cloud?
DSPM identifies high-risk data repositories, detects excessive permissions, and enables teams to remove unnecessary access, delete redundant data, and enforce governance policies.
6. Can DSPM help secure SaaS applications like Microsoft 365?
Yes. DSPM scans SaaS platforms to identify sensitive data, detect overexposed files, and analyze sharing permissions, helping organizations secure data across collaboration tools.
7. How does DSPM support AI data governance in cloud environments?
DSPM helps organizations discover and classify sensitive data before it enters AI systems, including training datasets and RAG pipelines. This reduces the risk of exposing regulated data in AI outputs.
8. What are the biggest risks in cloud data security today?
The biggest risks include lack of visibility into sensitive data, over-permissioned access, data sprawl across environments, and uncontrolled data flowing into AI systems.
9. How do organizations get started with DSPM for cloud security?
Organizations should begin by discovering sensitive data across cloud and SaaS environments, classifying it with context, analyzing access, and prioritizing remediation based on risk.
10. Is DSPM a replacement for existing cloud security tools?
No. DSPM complements existing tools. It provides data-level visibility and context, while tools like CSPM, IAM, and DLP enforce controls.
Why DSPM Is Essential for UK Cloud Security
UK enterprises operate under increasing pressure:
- UK GDPR requirements
- growing AI adoption
- expanding cloud environments
Security leaders must protect sensitive data across all three.
DSPM provides the foundation to do that.
It enables organizations to:
- understand their data
- control access
- reduce exposure
- support compliance
The Future of Cloud Data Security
Cloud adoption will continue to grow.
Data will continue to spread.
AI systems will continue to rely on enterprise data.
Security strategies must evolve.
Organizations that focus only on infrastructure will fall behind.
Organizations that focus on data visibility and control will lead.
DSPM defines that shift.
See How BigID Discovers and Secures Cloud Data at Scale.