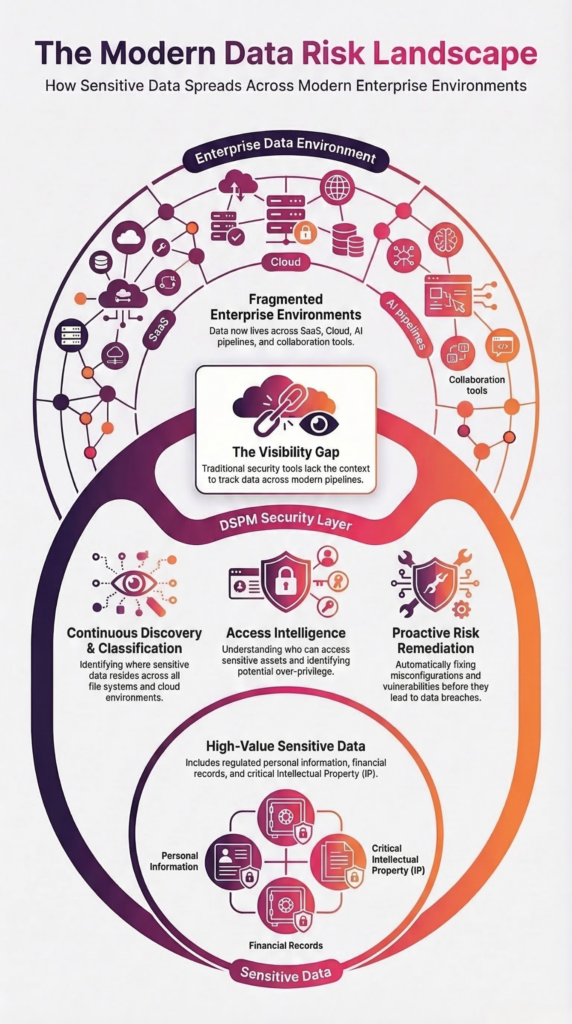
UK organizations face a growing challenge managing sensitive data across cloud, SaaS, and AI environments. This challenge has accelerated adoption of Data Security Posture Management (DSPM).
Many enterprises still rely on tools built for structured databases and network boundaries. Those tools miss the reality of modern data environments.
Security leaders now ask a different question:
Where does our sensitive data live, and who can access it?
That question drives the rapid rise of Data Security Posture Management (DSPM) across UK enterprises.
DSPM helps organizations discover, classify, and secure sensitive data across modern data environments. Instead of focusing only on infrastructure, DSPM focuses on the data itself.
For CISOs, privacy leaders, and security architects, DSPM delivers something most security tools cannot: complete visibility into sensitive data risk.
At a Glance
• Data growth across SaaS, cloud, and AI creates visibility gaps for UK enterprises.
• Traditional security tools cannot identify or govern sensitive data.
• DSPM provides complete visibility into data risk across modern environments.
• Organizations use DSPM to reduce exposure and operationalize data security.
Best for: Security leaders evaluating DSPM adoption.
The Data Security Challenges Driving DSPM Adoption in the UK
Data growth has accelerated across every sector in the UK economy.
Organizations store sensitive data in:
- SaaS platforms such as Microsoft 365 and Google Workspace
- Cloud environments like AWS and Azure
- Collaboration platforms such as SharePoint and Slack
- AI pipelines and data lakes
- File systems and legacy repositories
These environments generate massive volumes of unstructured data.
Most organizations cannot answer critical questions such as:
- What sensitive data exists across our environment?
- Where does that data reside?
- Who can access it?
- Should they have access?
Security teams lack the tools to answer those questions consistently.
DSPM changes that.
What Is Data Security Posture Management (DSPM)?
Data Security Posture Management (DSPM) is a security approach that helps organizations discover sensitive data, classify it accurately, analyze access risk, and reduce data exposure across cloud, SaaS, and unstructured environments.
DSPM platforms provide three essential capabilities:
1. Data Discovery
Organizations locate sensitive data across cloud platforms, SaaS applications, and unstructured repositories.
2. Data Classification
Security teams understand what type of data exists, including:
- personal data
- financial records
- intellectual property
- regulated information
3. Access Intelligence
Organizations analyze who can access sensitive data and determine whether those permissions create risk.
Together, these capabilities allow security teams to prioritize and reduce data exposure.
Why UK Regulations Are Driving DSPM Adoption
Regulation has played a major role in DSPM adoption across the UK.
UK GDPR places strict requirements on organizations to understand and protect sensitive personal data.
Several principles make DSPM essential:
Data Minimization
Organizations must limit the collection and storage of personal data.
DSPM helps security teams identify unnecessary or redundant data.
Accountability
Organizations must demonstrate how they manage and protect sensitive information.
DSPM provides detailed visibility into sensitive data locations and access.
Breach Risk Reduction
Regulators increasingly scrutinize data breaches that involve excessive access or poor data governance.
DSPM helps organizations identify high-risk data exposure before incidents occur.
For security leaders, DSPM helps translate regulatory requirements into operational controls.
Real-World DSPM Use Cases for UK Enterprises
DSPM delivers value across multiple security and compliance scenarios.
Securing Cloud Data Exposure
Cloud environments often contain sensitive data stored in poorly governed repositories.
DSPM identifies:
- exposed storage buckets
- misconfigured data permissions
- unclassified sensitive data
Security teams can immediately prioritize the highest-risk exposures.
Protecting Sensitive Data in AI Pipelines
AI adoption continues to grow across UK enterprises.
Many AI projects ingest enterprise data without sufficient governance.
DSPM helps organizations:
- identify sensitive data used in training datasets
- detect regulated data entering AI pipelines
- govern data used in RAG systems
This prevents sensitive information from appearing in AI outputs.
Reducing Insider Risk
Many data breaches involve excessive internal access rather than external attacks.
DSPM analyzes access patterns to identify:
- over-permissioned data repositories
- stale access privileges
- shared sensitive data
Security teams can quickly remove unnecessary access.
Accelerating Data Breach Response
When incidents occur, security teams need to answer critical questions quickly:
- What sensitive data was exposed?
- Who had access to it?
- What regulatory obligations apply?
DSPM allows organizations to identify affected data and respond faster.
Why Legacy Security Tools Fall Short
Traditional security tools focus on infrastructure rather than data.
Examples include:
- network monitoring tools
- endpoint protection
- legacy DLP systems
These tools lack visibility into modern data environments.
They cannot answer key questions such as:
- What sensitive data exists across SaaS environments?
- Which unstructured repositories contain regulated data?
- Which users have access to high-risk information?
DSPM fills that gap by focusing on data visibility and governance.
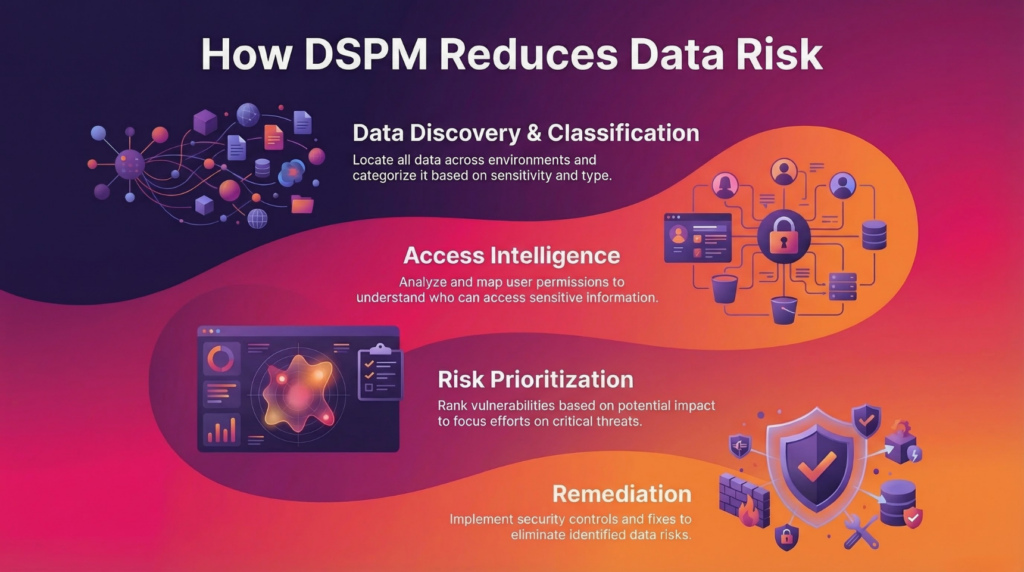
How Security Leaders Operationalize DSPM
Successful DSPM programs follow a structured approach.
Step 1: Discover Sensitive Data
Organizations scan environments to identify where sensitive data resides.
Discovery should cover:
- SaaS platforms
- cloud environments
- collaboration tools
- unstructured repositories
Step 2: Classify Data with Context
Classification determines what type of sensitive data exists.
Effective classification includes:
- pattern recognition
- contextual analysis
- machine learning classification
Context allows organizations to understand data risk more accurately.
Step 3: Analyze Data Access
Security teams analyze who can access sensitive data.
Access intelligence identifies:
- excessive permissions
- shared data exposure
- insider risk scenarios
Step 4: Remediate Data Risk
Once organizations identify risk, they can take action.
Common remediation actions include:
- removing unnecessary access
- moving data to secure repositories
- deleting unnecessary sensitive data
This transforms DSPM from visibility into active risk reduction.
Frequently Asked Questions About DSPM and Unstructured Data in the UK
1. What is Data Security Posture Management (DSPM)?
DSPM helps organizations discover sensitive data, classify it, analyze access, and reduce exposure across cloud, SaaS, and unstructured environments. It focuses on the data itself rather than infrastructure.
2. Why is unstructured data a challenge for UK enterprises?
Unstructured data grows rapidly across platforms like SharePoint, Google Drive, and cloud storage. Organizations often lack visibility into what data exists, where it resides, and who can access it, which creates significant risk.
3. How does DSPM help manage unstructured data?
DSPM scans unstructured data repositories, identifies sensitive information, classifies it with context, and analyzes access. This allows organizations to reduce risk and enforce governance across large volumes of data.
4. How does DSPM support AI data governance?
DSPM helps organizations discover and classify sensitive data before it enters AI pipelines. This reduces the risk of exposing regulated or confidential information in training datasets, RAG systems, or AI outputs.
5. Why are UK enterprises adopting DSPM now?
UK enterprises face rapid data growth, increased cloud and AI adoption, and stricter regulatory requirements. DSPM provides the visibility and control needed to manage data risk across modern environments.
6. How does DSPM differ from traditional security tools?
Traditional tools focus on infrastructure, networks, or endpoints. DSPM focuses on data. It shows what data exists, where it lives, and who can access it, which helps organizations manage data risk more effectively.
7. Can DSPM help reduce data breach risk?
Yes. DSPM identifies high-risk exposures such as over-permissioned access, unclassified sensitive data, and unsecured repositories. Security teams can take action to reduce risk before a breach occurs.
8. How does DSPM support UK GDPR compliance?
DSPM helps organizations discover personal data, classify regulated information, and control access. This supports data minimization, accountability, and breach risk reduction under UK GDPR.
9. What types of data can DSPM discover?
DSPM discovers structured and unstructured data, including personal data, financial records, intellectual property, and other regulated information across cloud, SaaS, and on-prem environments.
10. What are the first steps to operationalize DSPM?
Organizations should start by discovering sensitive data, classifying it with context, analyzing access, and then remediating risk. This structured approach helps scale data governance and security effectively.
Why DSPM Matters for the Future of AI and Data Security
Data now drives almost every digital initiative.
Organizations rely on data to power:
- analytics
- AI systems
- digital services
- automation
However, those same initiatives increase the potential impact of data exposure.
A single misconfigured repository can expose millions of records.
DSPM helps security teams govern data before it creates risk.
Organizations that invest in DSPM gain three strategic advantages:
- stronger regulatory compliance
- reduced data breach exposure
- safer AI adoption
Why DSPM Will Become Essential for UK Data Security
UK enterprises now manage sensitive data across cloud platforms, SaaS environments, and AI systems. Security teams need visibility into that data before risk escalates. DSPM gives organizations the ability to discover, classify, and govern sensitive data at scale.
The Future of Data Security in the UK
The UK continues to strengthen its focus on data governance, AI oversight, and privacy protection.
Security leaders must adapt their approach.
Organizations that rely on traditional security tools struggle to manage modern data environments.
DSPM introduces a new security model:
protect the data itself, not just the infrastructure around it.
For UK enterprises navigating complex data ecosystems, DSPM has quickly become a foundational security capability.
See How BigID Discovers and Secures Sensitive Data at Scale