Quantum computing is coming, but most organizations are preparing for it the wrong way.
Auf einen Blick
- Quantum risk is already underway through “harvest now, decrypt later” attacks
• Most organizations are over-focusing on post-quantum cryptography
- The bigger gap is lack of visibility into where sensitive data is encrypted
• Not all encrypted data carries equal risk
- Quantum readiness starts with understanding data exposure, not just upgrading algorithms
- A data-centric approach enables targeted, risk-based prioritization
• Organizations can act now by discovering encrypted data, mapping keys, and assessing exposure
The conversation today is dominated by post-quantum cryptography. That includes new algorithms, future standards, and migration strategies. While those efforts are important, they overlook a more immediate issue.
You can’t prepare for quantum risk if you don’t understand your data.
Before replacing encryption, organizations need to know where it’s used, what it protects, and what happens if it fails. Without that visibility, even the most advanced cryptographic strategy will fall short.
The Real Risk: “Harvest Now, Decrypt Later”
Quantum risk isn’t just a future problem. It is already in motion.
Attackers are collecting encrypted data today with the expectation that future quantum capabilities will allow them to decrypt it. This “harvest now, decrypt later” approach turns long-lived data into a delayed liability.
Sensitive data that appears secure today, such as customer records, financial data, and intellectual property, may be exposed in the future without any new breach occurring.
This changes the conversation. Encryption is no longer just about protecting data in the present. It is about understanding how that data could be exposed over time.
Why Encryption Visibility Is the Missing Piece
Most organizations rely heavily on encryption, but few have a clear understanding of how it is used across their environment.
Basic questions often go unanswered:
- Where is sensitive data encrypted?
- What encryption standards are protecting it?
- Where are keys and secrets stored?
- Who has access to encrypted data and cryptographic assets?
Traditional tools focus on encryption deployment, such as certificates, protocols, and configurations. However, they lack context. They do not connect encryption to the sensitivity of the data or the business impact if protection fails.
Without this connection, organizations treat all encrypted data the same, even though some data carries far greater risk than others.
Quantum Readiness Is a Data Problem
Preparing for quantum is not just about upgrading encryption. It is about understanding exposure.
A data-centric approach shifts the focus from where encryption exists to what actually matters. That is identifying which sensitive data is at risk if encryption is broken.
- “Where is encryption used?”
Zu - “Which sensitive data is at risk if encryption fails?”
This shift allows organizations to move beyond generic planning and toward targeted, risk-based action.
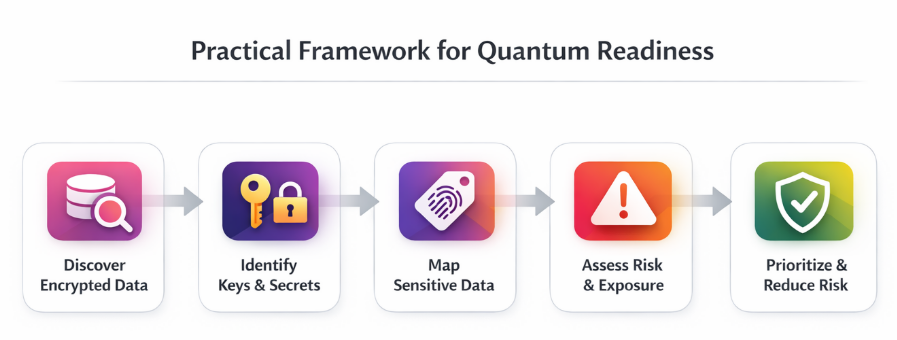
A Practical Framework for Quantum Readiness
Organizations do not need to wait for quantum computing to mature. They can take action now by focusing on data visibility and risk context.
This framework provides a structured approach to understanding and prioritizing quantum risk.
1. Discover Encrypted Data
The first step is visibility. Most organizations lack a complete inventory of where encryption is applied across their environments.
Without this foundation, it is difficult to assess exposure or understand the scope of potential risk.
Focus on identifying:
- Encrypted data across cloud, SaaS, and on-prem systems
- Structured and unstructured data stores
- Data used in analytics and AI pipelines
Gain visibility into sensitive data across your environment and identify where encryption risk exists.
2. Identify Keys and Secrets
Encryption is only as strong as the keys that protect it. In many environments, keys and secrets are distributed across systems, embedded in code, or accessible to more users and services than necessary.
Gaining control requires understanding where these assets exist and how they are managed.
Dies umfasst:
- Encryption keys and key management systems
- API keys, tokens, and credentials
- Secrets embedded in applications and pipelines
3. Map Sensitive Data to Encryption
Not all encrypted data carries equal risk. The priority is understanding which sensitive data depends on encryption for protection.
This step connects technical controls to business impact and helps organizations focus on what matters most.
Look to map:
- PII, PHI, and financial data
- Intellectual property and proprietary datasets
- Regulated and high-value data assets
4. Assess Exposure and Risk
With visibility into both data and keys, organizations can evaluate where meaningful risk exists. Exposure often results from a combination of factors, including weak encryption, broad access, and data sprawl.
The goal is to identify where these risks intersect.
Evaluate:
- Weak or outdated encryption methods
- Overexposed or poorly managed keys
- Excessive or unnecessary access to encrypted data
5. Prioritize and Reduce Risk
Quantum readiness ultimately requires action. Once risks are identified, organizations can focus on reducing exposure where it matters most instead of trying to address everything at once.
This creates a more practical and scalable approach.
Prioritize efforts to:
- Reduce unnecessary data and key sprawl
- Strengthen protection around high-risk datasets
- Prepare for future cryptographic upgrades
Why This Matters Now in The Age of AI
AI increases the urgency of quantum readiness.
Sensitive data is no longer just stored. It is actively used to train models, power copilots, and drive automated decisions. This expands the potential impact of exposure beyond storage systems into AI-driven workflows.
If encryption protecting this data is broken, the consequences extend further and faster.
Organizations need to understand not just where data lives, but how it flows into AI systems and how it is accessed and used.
Start with What You Can Control
Organizations do not need to solve quantum computing to begin preparing for it.
They can start by improving visibility into encrypted data, understanding where keys and secrets exist, and identifying which data carries the highest risk.
Those that take a data-first approach today will be better positioned to adapt as quantum capabilities evolve.
Abschluss
Quantum computing will change the future of encryption, but the bigger challenge is understanding your exposure today. Most organizations do not yet have visibility into where encrypted data lives, what it protects, or how it could be exposed if encryption fails.
Quantum readiness starts with clear insight into your data, your keys, and your risk.
Want to understand your organization’s exposure to quantum risk? Schedule a 1:1 to assess your data security posture.