Modern data security is no longer just about monitoring access to files. It requires understanding where sensitive data lives across cloud, SaaS, and AI systems and reducing the risk created by data exposure.
Most breaches occur not because organizations lack visibility, but because sensitive data is overexposed across cloud, SaaS, and hybrid environments.
Security teams evaluating platforms like Varonis and BigID must decide whether their priority is monitoring user activity ou reducing exposure around sensitive data itself.
At a Glance
- Varonis focuses on monitoring user activity and detecting suspicious access behavior
- BigID focuses on discovering sensitive data and reducing exposure risk across environments
- DSPM platforms like BigID help identify overexposed data, prioritize risk, and reduce the data attack surface
- Varonis is strongest in file systems and access monitoring, while BigID provides visibility across cloud, SaaS, databases, and AI systems
- Organizations prioritizing modern data security and exposure reduction often adopt DSPM platforms like BigID
This comparison is most relevant for organizations evaluating how to reduce data exposure across cloud, SaaS, and AI environments.
Security teams today must answer critical questions:
- Where does sensitive data live?
- Qui y a accès ?
- Is that access appropriate?
- Is the data exposed or at risk?
Two platforms frequently evaluated together are Varonis et BigID. Both help organizations reduce data risk, but they approach the problem from different angles.
Varonis focuses primarily on monitoring user behavior and file access activity to detect insider threats.
BigID se concentre sur discovering sensitive data, identifying exposure risk, and reducing the data attack surface across cloud, SaaS, and on-prem environments à travers Gestion de la sécurité des données (DSPM).
Understanding these differences can help determine which platform aligns best with your organization’s security strategy.
Varonis vs BigID: Monitoring Access vs Reducing Data Exposure
Before we dive into the nitty-gritty, here’s a quick view of how the two compare in terms of features:
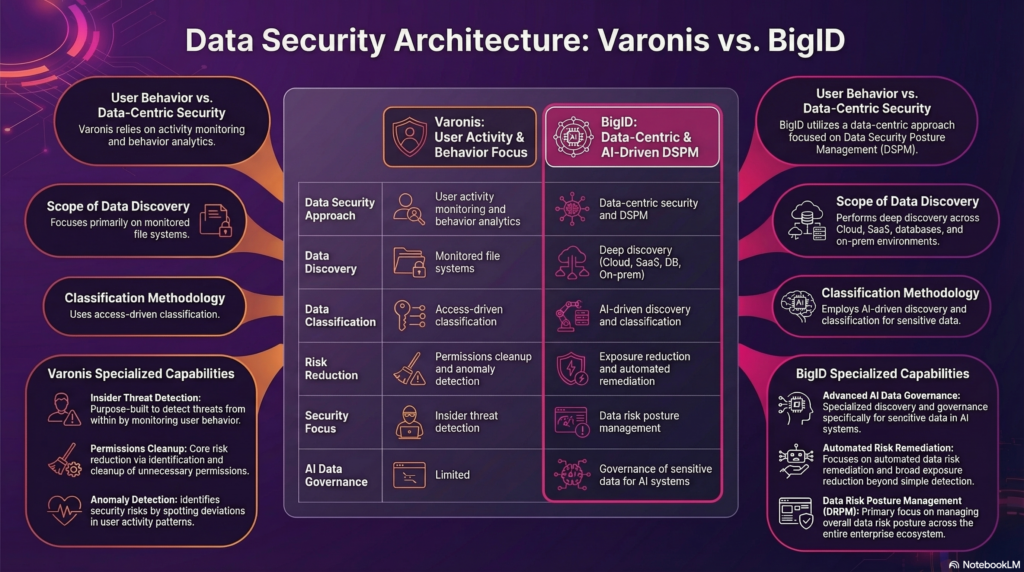
This comparison reflects a broader shift in data security from monitoring access to reducing exposure.
Qu’est-ce que la gestion de la posture de sécurité des données (DSPM) ?
Data Security Posture Management (DSPM) helps organizations discover sensitive data, assess exposure risk, and reduce data security risk across cloud, SaaS, and on-prem environments.
Traditional security tools often focus on infrastructure, endpoints, or user activity. DSPM focuses directly on the data itself.
DSPM platforms identify:
- Où résident les données sensibles
- Qui y a accès
- Whether that access creates exposure risk
DSPM platforms typically provide capabilities such as:
- Découverte de données sensibles across cloud, SaaS, and on-prem systems
- AI-based classification of regulated and sensitive data types
- Risk prioritization based on data sensitivity and exposure
- Detection of overexposed or misconfigured data stores
- Remédiation automatisée of data security risks
Unlike traditional discovery tools, DSPM platforms also identify exposure risk, prioritize remediation, and reduce the attack surface around sensitive data.
As organizations store more data across multi-cloud, SaaS platforms, and AI systems, security teams need visibility into where sensitive data resides and how it is exposed.
This is where DSPM platforms like BigID play a critical role.
How BigID Delivers Data Security Posture Management
BigID provides one of the most advanced DSPM platforms, helping organizations understand and reduce data risk across their entire data landscape.
BigID moves beyond visibility to actively reduce exposure across sensitive data.
Unlike traditional access monitoring tools, BigID focuses on the data itself and the risk created by its exposure.
Deep Data Discovery
BigID scans structured and unstructured data across:
- plateformes cloud
- Applications SaaS
- bases de données
- file systems
- entrepôts de données
This provides a complete inventory of sensitive data across modern environments.
Classification pilotée par l'IA
Machine learning models identify:
- les informations personnellement identifiables (PII)
- données financières
- healthcare data
- regulated and confidential information
This allows security teams to understand what data matters most.
Exposure Risk Identification
BigID does more than locate sensitive data.
The platform identifies:
- Données sensibles surexposées
- Excessive access permissions
- Toxic combinations of sensitive data
- Stale or unused sensitive data
These risks significantly increase breach exposure.
Remédiation automatisée des risques
Security teams can prioritize and remediate risks by:
- reducing excessive permissions
- removing unnecessary data access
- deleting stale sensitive data
- improving governance controls
This helps organizations reduce their data attack surface.
DSPM vs Access Monitoring Tools
Varonis and DSPM platforms like BigID address different layers of the data security problem.
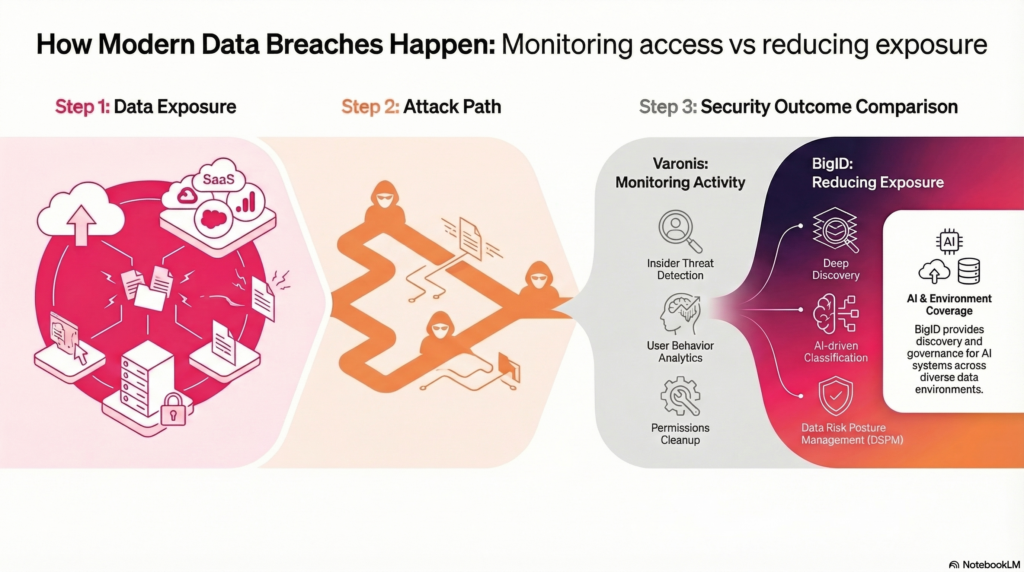
Coverage Across Modern Data Environments
Another key difference is platform coverage.
Varonis primarily focuses on monitoring:
- file systems
- plateformes de collaboration
- user activity
DSPM platforms like BigID provide visibility across:
- plateformes cloud
- Applications SaaS
- databases and data warehouses
- données non structurées et structurées
- environnements hybrides
This broader coverage allows security teams to identify sensitive data exposure across their entire data ecosystem. This is especially important as sensitive data increasingly resides outside traditional file systems.
Securing Data Used by AI Systems
Organizations adopting generative AI and machine learning systems face a new data security challenge: understanding what sensitive data is used by AI applications.
AI models are often trained on large datasets that may contain:
- les informations personnelles identifiables (IPI)
- données financières
- confidential intellectual property
- données réglementées
Without proper governance, this data can be unintentionally exposed through AI outputs or embedded within AI training pipelines.
DSPM platforms help organizations identify and govern the data used by AI systems.
By discovering sensitive data across environments and applying classification and governance policies, security teams can better understand what data is flowing into AI applications and reduce associated risks.
This capability is becoming increasingly important as organizations implement AI governance frameworks and AI TRiSM stratégies.
BigID vs Varonis: Cost, Key Features, and Capabilities
Selecting the right platform requires more than comparing features.
Organizations should also evaluate:
- deployment flexibility
- couverture des données
- risk reduction capabilities
Below is a closer look at how each platform addresses data security challenges.
BigID
BigID delivers Data Security Posture Management (DSPM), sensitive data discovery, classification, and automated data risk remediation on a unified platform.
Security teams use BigID to:
- understand where sensitive data lives
- identify exposure risks
- reduce data attack surface
Best For
- Gestion de la sécurité des données (DSPM)
- Découverte et classification des données sensibles
- Data risk remediation and exposure reduction
- Privacy automation and regulatory compliance workflows
Varonis
Varonis focuses primarily on monitoring user behavior and managing access permissions to detect insider threats and suspicious activity.
The platform analyzes file activity, identifies abnormal behavior patterns, and helps organizations reduce excessive access permissions.
Best For
- Gouvernance de l'accès aux données
- User behavior analytics
- Insider threat detection
How Organizations Evaluate DSPM vs Access Monitoring
Many organizations evaluate DSPM platforms and access monitoring tools together.
DSPM platforms help security teams:
- discover sensitive data across modern environments
- identify exposure risks
- reduce the attack surface around sensitive data
Access monitoring tools focus on:
- detecting suspicious user activity
- analyzing behavioral anomalies
- monitoring access patterns
Security teams often deploy DSPM platforms to reduce exposure risk before attackers can exploit it.
Why Organizations Move from Access Monitoring to DSPM
Many organizations initially adopt access monitoring tools to gain visibility into user activity and permissions. These tools help detect suspicious behavior and identify insider threats.
However, as data environments become more complex, security teams often encounter limitations.
Sensitive data is no longer confined to file systems. It is distributed across cloud platforms, SaaS applications, databases, and AI systems.
This shift creates new challenges:
- Limited visibility into where sensitive data exists across environments
- Difficulty identifying overexposed or misconfigured data
- Increasing risk from stale data and excessive permissions
- Lack of insight into sensitive data used in AI systems
To address these challenges, organizations are adopting Data Security Posture Management (DSPM) platforms.
DSPM platforms help security teams:
- Discover sensitive data across cloud, SaaS, and hybrid environments
- Identify exposure risks based on data sensitivity and access
- Prioritize and remediate high-risk data exposures
- Reduce the data attack surface before threats occur
Rather than focusing only on monitoring activity, DSPM shifts the focus to reducing exposure risk at the data level.
As a result, many organizations use DSPM platforms like BigID to complement or expand beyond access monitoring tools as part of a modern data security strategy.
Choose BigID When You Need
- Deep discovery of sensitive and regulated data
- Gestion de la sécurité des données (DSPM)
- Visibility across cloud, SaaS, and hybrid environments
- Automated data risk remediation
- Privacy automation and regulatory compliance workflows
Choose Varonis When You Need
- Monitoring of user activity and permissions
- Behavioral analytics for insider threats
- Access governance within file systems and collaboration platforms
Final Verdict
Varonis and BigID address different aspects of data security.
Varonis focuses on monitoring user behavior and detecting suspicious access activity.
BigID focuses on discovering sensitive data, identifying exposure risk, and reducing the data attack surface across modern data environments.
Organizations prioritizing data visibility, exposure reduction, and privacy operations often adopt DSPM platforms like BigID.
BigID vs Varonis: Frequently Asked Questions
Is BigID better than Varonis?
The answer depends on your security priorities.
Organizations focused on discovering sensitive data and reducing exposure across cloud and SaaS environments often choose BigID.
Organizations focused on monitoring user behavior and access activity may consider Varonis.
Is BigID a DLP tool?
No. BigID is not a traditional Data Loss Prevention (DLP) tool.
BigID provides data discovery, classification, and Data Security Posture Management (DSPM) to help organizations identify sensitive data and reduce exposure before data loss occurs.
Can organizations migrate from Varonis to BigID?
Yes. Many organizations adopt BigID to expand visibility into sensitive data across cloud, SaaS, and modern data environments.
Migration strategies vary depending on infrastructure and security priorities.
Implement Data-Centric Security With BigID
Organizations prioritizing data visibility, exposure reduction, and modern data security across cloud, SaaS, and AI environments often adopt DSPM platforms like BigID.